“Big Data Security… Yeah, what about it?”
“Big Data Security… Yeah, what about it?”
by Wilco van Ginkel, *Security, November 22, 2014
As with any new trend, technology or ‘anything disruptive’, security becomes a key question. Unfortunately, most of the time, not right from the beginning. But somewhere along the way it becomes a discussion topic, whether we like it or not.
This is especially true for Big Data, given that we have become a data-driven society. Which raises questions about privacy, big brother is spying/watching us, and data ownership, to name a few.
Data security is definitely not something new and we are tying to get our heads around this for decades. Given the ‘Big Data movement’, it begs the question whether Big Data security is really that different than… It is and it is not.
It is not, because basic data quality requirements (e.g., accuracy, veracity, security) still hold true for Big Data, no matter ‘how big’. It is, as there are certainly differences, which make Big Data security even more challenging. A few examples are:
- Data Volume & Velocity: there is simply much more data we have to deal with. And seemingly, at a fast growing pace.
- Data democratization: producing and consuming data is at everybody’s finger tips. Thanks to cheap, cost-effective and easy to use technologies, like mobile and Cloud.
- Big Data Technologies: these technologies make it possible to combine massive sets of data, and, more important, get different views on data. Particularly integrated views, which were not possible before and which may not always be desirable from, say, a privacy perspective.
- Data is borderless: given that there is no standard international data legislation, this leads to even more challenges in the field of data protection and privacy on a global scale.
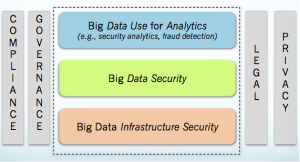
In order to get our heads around Big Data Security, the following framework might be a good start:
As shown in the framework, Big Data Security is a three-prong approach:
- Big Data Infrastructure Security: the security of the underlying IT infrastructure (e.g., Cloud) on top of which Big Data services live (e.g., storage, analytics).
- Big Data Security: this is about the security of the data itself. Think: encryption of data, access to data.
- Big Data Use for Analytics: this is about how we can use Big Data itself in our security analytics. With the goal to come up with better analytical services related to, in this case, security (e.g., better fraud detection, faster and more accurate intrusion detection).
These layers are surrounded by other pillars which go across, like compliance, governance, legal and privacy.
As this is a complex and vast evolving field, the Cloud Security Alliance Big Data Working Group (https://cloudsecurityalliance.org/research/big-data/) has taken the initiative to research this field. The group has published (and will continue to do so) different Big Data Security white papers, like Big Data Taxonomy, Top Ten Big Data Security and Privacy Challenges, and Big Data Analytics for Security Intelligence. Please see https://cloudsecurityalliance.org/research/big-data/#_downloads to download these papers.